On August 27, 2025, the U.S. Treasury’s Office of Foreign Assets Control (OFAC) dropped a major move: it sanctioned a Russian national, a North Korean operative, and two companies tied to a global network that stole over $2.1 billion in cryptocurrency in just the first half of the year. This wasn’t a one-off. It was the latest step in a relentless, year-long campaign targeting North Korea’s most dangerous and underreported revenue stream - crypto theft disguised as remote IT work.
Here’s the brutal truth: North Korea isn’t just hacking exchanges anymore. It’s embedding its agents inside U.S. tech companies - including crypto startups - using fake identities, stolen documents, and remote work platforms to steal data, demand ransom, and siphon off millions in stablecoins. And it’s working. The money doesn’t vanish into the blockchain. It gets converted to cash, shipped overseas, and funneled straight into weapons programs.
How North Korea’s IT Worker Scam Works
Imagine a freelance software developer on Freelancer.com, hired by a Silicon Valley startup to build a smart contract. They deliver on time. They’re responsive. They use GitHub with a clean history. They even have a Medium blog about Web3 architecture. Sounds legit, right? Except this person doesn’t exist.
They’re a North Korean operative. Their identity - ‘Joshua Palmer,’ ‘Alex Hong,’ or one of dozens of reused personas - was built from stolen personal data. Their resume? Fabricated. Their LinkedIn? Fake. Their work? Real enough to pass vetting. But while they’re coding, they’re also mapping the company’s security gaps, logging credentials, and installing backdoors.
These workers are placed in companies that rely heavily on remote teams - especially crypto firms where hiring is fast, background checks are light, and payroll is often done in USDC or ETH. Once they’re in, they start collecting payments. Not for work. For fraud. They invoice for services never rendered, or they’re paid for work that’s just a cover. The crypto hits their wallet. Then it moves - through dozens of intermediate addresses, mixing services, and self-hosted wallets - before landing in the hands of senior DPRK operatives like Kim Sang Man and Sim Hyon Sop, both already on OFAC’s sanctions list.
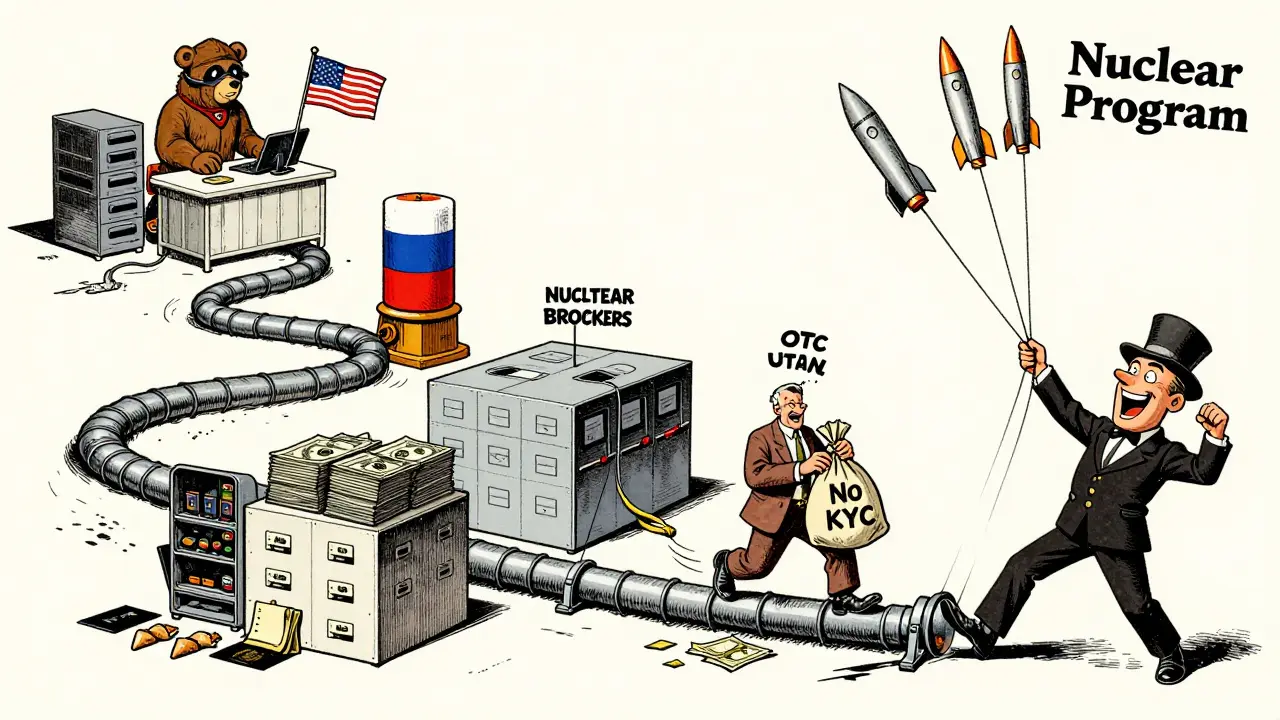
The Money Trail: From ETH to Cash
The stolen funds don’t stay digital. That’s the key. North Korea doesn’t need Bitcoin to buy missiles. It needs U.S. dollars. So the crypto gets converted.
Investigators found that Kim Ung Sun, one of the newly sanctioned individuals, personally handled over $600,000 in crypto-to-cash conversions. He used OTC brokers - some based in Russia, others in the UAE - who didn’t ask questions. These brokers, in turn, were linked to shell companies in China and Laos. The cash was then moved through third-country banks, often with forged invoices for ‘IT consulting’ or ‘software licensing.’
The Department of Justice filed a civil forfeiture case in June 2025, seizing $7.7 million in digital assets - including ETH, USDC, and even high-value NFTs - tied to this network. One wallet alone had over 120 incoming transactions from compromised U.S. companies. Each one was a small drip. Together, they made a flood.
Who Got Sanctioned? The Key Players
OFAC didn’t go after random addresses. They went after the people and companies making it possible:
- Vitaliy Sergeyevich Andreyev - A Russian national who helped move funds and provided infrastructure, including servers and IP addresses.
- Kim Ung Sun - The North Korean operative directly managing financial transfers from stolen crypto.
- Shenyang Geumpungri Network Technology Co., Ltd - A front company in China, posing as a legitimate IT outsourcing firm.
- Korea Sinjin Trading Corporation - A trading entity used to disguise crypto payments as legitimate business transactions.
These weren’t isolated actors. They were nodes in a network that also includes Korea Sobaeksu Trading Company, Chinyong Information Technology Cooperation Company, and at least seven other entities sanctioned since 2023. All of them operate under the same model: hire remote workers, collect crypto, launder it, send cash to Pyongyang.
Why This Is Different From Regular Hacking
Most cyberattacks are one-time hits: ransomware, phishing, data breaches. This is a system. It’s not just stealing money. It’s stealing trust.
North Korea’s IT workers aren’t breaking in. They’re being hired. They’re on Slack. They’re in Zoom meetings. They’re getting performance reviews. And while they’re doing real work - sometimes even good work - they’re gathering intel on internal systems, employee access levels, and wallet storage practices. One company lost $1.2 million not because their wallet was hacked, but because their ‘remote developer’ quietly copied the seed phrase during a system update.
It’s espionage disguised as outsourcing. And it’s working because no one expects a North Korean to be on their team.
The Global Web: Russia, China, UAE
This isn’t a North Korean problem. It’s a global blind spot.
The infrastructure supporting these operations spans continents. Russian servers host the fake GitHub profiles. Chinese firms supply the fake IDs and passports. UAE-based OTC brokers convert crypto to cash without KYC. And the money flows through shell companies in Laos and Vietnam.
OFAC’s August 2025 sanctions specifically named Russian and UAE-linked entities because they’re critical to the laundering chain. Without these third-country facilitators, the whole scheme collapses. That’s why the U.S. is now pressuring foreign governments - Japan, South Korea, and others - to shut down these cross-border pipelines.
Law enforcement agencies like the FBI and HSI have seized wallets, tracked transactions, and even worked with blockchain analytics firms like TRM Labs to build real-time dashboards of sanctioned addresses. The goal isn’t just to freeze funds - it’s to map the entire ecosystem so future sanctions can hit the next link before it even forms.

What This Means for Crypto Companies
If you run a crypto startup or hire remote developers, this isn’t a ‘foreign policy’ issue. It’s a security risk.
Here’s what you need to do:
- Verify identities beyond LinkedIn - Ask for government-issued ID, cross-check with phone records, and use third-party verification tools. Don’t rely on self-reported info.
- Monitor wallet activity - If a contractor’s payment address has ever been linked to a sanctioned entity (check OFAC’s list), cut ties immediately.
- Limit wallet access - Don’t give remote workers access to cold storage, admin keys, or multisig wallets. Use role-based access controls.
- Screen for red flags - Workers using only free email domains (Gmail, ProtonMail), no prior work history, or who refuse video interviews should raise alarms.
Companies that ignored these signs in 2024 are now facing lawsuits, regulatory fines, and reputational damage. One U.S.-based Web3 firm lost $3.4 million and had to shut down after their ‘lead blockchain engineer’ - later revealed to be a North Korean operative - drained their treasury wallet.
What’s Next?
OFAC isn’t done. In fact, they’re just getting started. The $2.1 billion stolen in 2025 is already being used to fund missile tests and nuclear development. The U.S. government has made it clear: if you’re helping North Korea launder crypto, you’re helping them build weapons.
More designations are coming. More arrests. More seizures. The blockchain is public. Every transaction leaves a trail. And with tools like TRM Labs and Chainalysis monitoring every movement, the days of hiding crypto theft behind fake identities are over.
The message is simple: If you’re working remotely for a company with ties to North Korea - even indirectly - you’re not just risking your job. You’re risking your freedom.
How did North Korea steal over $2.1 billion in crypto?
North Korea used remote IT worker schemes to infiltrate U.S. crypto and tech companies. Workers used fake identities to get hired, then stole data, copied wallet keys, and invoiced for non-existent services. Payments were made in USDC or ETH, then laundered through Russian, Chinese, and UAE intermediaries before being converted to cash and sent to North Korean military programs.
Who is Kim Ung Sun and why was he sanctioned?
Kim Ung Sun is a North Korean operative directly tied to converting stolen cryptocurrency into U.S. dollars. He facilitated at least $600,000 in transfers using front companies and OTC brokers. OFAC sanctioned him in August 2025 for his role in financing the DPRK’s weapons programs through crypto theft.
Can I get in trouble if I hire someone from North Korea unknowingly?
Yes. Even if you didn’t know, U.S. law requires companies to screen contractors against OFAC’s sanctions list. If you pay someone who’s later found to be linked to a sanctioned entity - even indirectly - you could face civil penalties, asset seizures, or criminal charges. Due diligence isn’t optional anymore.
What platforms are North Korean hackers using to find jobs?
They use global freelance platforms like Freelancer, Upwork, RemoteHub, CrowdWorks, and WorkSpace.ru. They also create fake GitHub profiles and Medium blogs to build credibility. Many use stolen identities from Eastern Europe and Southeast Asia to appear as local workers.
How can I check if a contractor is linked to North Korea?
Use OFAC’s sanctions list and blockchain analytics tools like TRM Labs or Chainalysis. Check the crypto addresses they use for payments. If any address has ever interacted with a sanctioned wallet (like those linked to Kim Sang Man or Andreyev), avoid them. Also, verify identity with multiple documents and video calls - never rely on documents alone.


Elizabeth Choe
February 14, 2026 AT 04:34Okay but like… imagine being a crypto founder and hiring someone who’s literally a DPRK spy. They’re coding your smart contracts while mapping your wallet keys. I mean, it’s like Netflix’s Dark meets Silicon Valley. And the scariest part? You’d never know. They’re probably better at Git commits than your actual dev team. 🤯
Claire Sannen
February 15, 2026 AT 23:59This is terrifyingly plausible. The fact that North Korea is using freelance platforms as a vector for espionage changes everything. We’ve been treating remote work as a convenience, not a security vulnerability. Time to overhaul hiring protocols across the industry.
Sakshi Arora
February 17, 2026 AT 07:22Michelle Cochran
February 17, 2026 AT 12:50It’s not just about crypto-it’s about the erosion of trust in digital labor. We’ve normalized hiring strangers with no verifiable identity, and now we’re paying the price. This isn’t espionage. It’s betrayal of the very idea of collaboration. And we let it happen because we were too busy optimizing for speed.
monique mannino
February 18, 2026 AT 17:45OMG I just realized-my last contractor used ProtonMail and never did a video call. 😳 I’m checking their wallet right now. Also, if you’re hiring devs on Upwork and don’t verify their ID with a government document + selfie holding a paper with today’s date… you’re basically handing your keys to a ghost.
krista muzer
February 19, 2026 AT 09:50I’ve been thinking about this a lot lately. The whole remote work boom was supposed to democratize opportunity, right? But what if it’s just opening the door for state-sponsored actors to slip in under the radar? I mean, imagine a kid in Pyongyang with a stolen Canadian passport, working 8 hours a day on Zoom while quietly stealing your private keys. It’s dystopian but… it’s already happening. We need to stop pretending that ‘flexibility’ means ‘no checks.’
Grace Mugambi
February 19, 2026 AT 10:45There’s a deeper layer here we’re ignoring. We treat these thefts as cybersecurity failures, but they’re really failures of imagination. We built a system where anyone can be anyone online-and we never asked whether that freedom should have boundaries. Maybe the real question isn’t how to stop them-but whether we want to keep building systems that make this possible.
Peggi shabaaz
February 21, 2026 AT 01:57so like… we’re all just one bad hire away from funding nukes? weird.
Ace Crystal
February 21, 2026 AT 07:44Let’s get real-this isn’t just about crypto. This is about the future of work. If we don’t fix identity verification now, every remote job in every industry will become a vector for exploitation. Time to stop being lazy and start building real checks. Your company’s next billion-dollar loss could be hiding in a GitHub profile.
Donna Patters
February 22, 2026 AT 15:14How is this even legal? We sanction entire nations for less. And yet, we allow North Korean operatives to infiltrate American tech firms under the guise of ‘freelance developers’? This is not a cybersecurity issue. It is a national security failure of monumental proportions. The U.S. government is asleep at the wheel.
Ben Pintilie
February 22, 2026 AT 22:24lmao imagine your ‘dev’ is a guy in Pyongyang who’s never seen a keyboard in real life
Robbi Hess
February 24, 2026 AT 16:37This is peak absurdity. We have blockchain analytics tracking every transaction, yet we still hire contractors based on a LinkedIn profile and a Gmail address. The irony is thick enough to spread on toast. Someone needs to fire the entire HR department at every crypto startup.
Keturah Hudson
February 26, 2026 AT 13:00As someone who’s worked with remote teams across five continents, I’ve seen the gaps. But this? This is beyond negligence. It’s systemic. We need international cooperation-not just sanctions. We need standardized digital identity verification. And we need to stop pretending that ‘good code’ means ‘good person.’
Crystal McCoun
February 27, 2026 AT 04:52Let’s be clear: if your remote developer uses a free email, refuses a video call, has no verifiable prior work history, and their wallet has ever touched a sanctioned address-you are not ‘being inclusive.’ You are endangering your company, your investors, and potentially national security. Please, for the love of all that is sane, implement mandatory ID verification. Use a third-party service. Pay the $20. It’s not optional anymore.
Christopher Wardle
February 28, 2026 AT 00:29There’s a philosophical tension here: between openness and security. The internet promised a borderless world. But borders are not just physical-they’re trust boundaries. When we erase those boundaries without replacement, we create vacuum spaces for exploitation. North Korea didn’t invent this; they weaponized our ideals.
Brittany Meadows
February 28, 2026 AT 14:54Wait… so the real plan was never to steal crypto? It was to make every tech company in America paranoid enough to stop hiring remotely? 😏 I mean… genius. I’m half-convinced this is a psychological operation to kill the gig economy. Either that, or we’re all just one bad GitHub commit away from WW3.
Desiree Foo
March 1, 2026 AT 22:46Anyone who hires someone without a background check, ID verification, and a blockchain address audit is not just negligent-they are complicit. This isn’t a gray area. It’s a crime scene. If you’re reading this and you’ve hired a remote dev without due diligence-you’re already on the wrong side of history.
Elijah Young
March 2, 2026 AT 11:13Just read the OFAC release. The fact that they named Russian and UAE entities means they’re targeting the entire pipeline. This isn’t about North Korea anymore-it’s about the global shadow economy that enables them. If you’re an OTC broker, a server host, or a passport forger, you’re now officially a target. Good.